Cyberwar and Insurers: Are we protected?
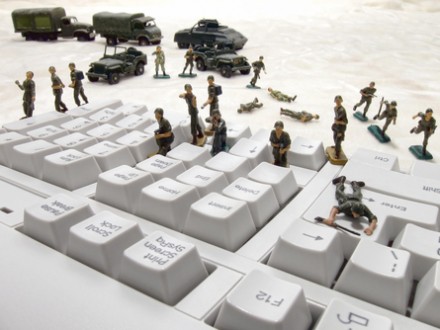
State-backed cyber-attacks have become a weapon of political destabilisation and low-intensity warfare. What is the insurance industry’s response to this cyber-warfare?
Cyberspace has become the new battleground for states. The war in Ukraine is a case in point. According to Check Point analysts, cyber-attacks on the Ukrainian government and military sector increased by 112% between February and August, following the Russian invasion. In addition, Ukraine’s corporate networks received more than 1,500 cyberattacks per week on average, far exceeding the global average of 1,124 cyberattacks per week.
This is not the only example. Some of the most active cybercriminal groups are known to be backed by Russia, China, North Korea or Iran. It seems clear that geopolitical tensions and conflicts between nations have entered a new era, where cyberwarfare is set to become increasingly prominent.
“The Swedish Security and Defence Industry Association recently produced a report revealing that state-sponsored cyber espionage activities now account for 25 per cent of the total. In other words, one in four cyber-attacks is promoted by governments,” says Eusebio Nieva, technical director of Check Point Software for Spain and Portugal.
“The main problem is that they have large resources and, therefore, the attacks are large and far-reaching,” says Álvaro Satrústegui, CEO of Exsel Underwriting Agency. Likewise, Benjamín Losada, specialised underwriter in cyber risks at Hiscox Spain, stresses that “states have the talent, tools and investment to carry out cyber attacks at the highest level, which translates into greater exposure of companies to risk”.
What are their goals?
Daniel Hernández, Director of Risk Advisory – Cyber at Deloitte, indicates that “the underlying motivation is a combination of economic factors, social influence and destabilisation of certain processes of the mechanisms of the healthy functioning of a society and the state that presents it”.
Nieva points out that these acts of cyberwarfare can have several intentions. “On the one hand, obtaining and gathering information. On the other hand, the exploration of vulnerabilities, detection mechanisms, etc. In other words, to test the security posture of the attacked party. Finally, the disruption of services or systems,” he explains. And he specifies that “the most common case is to obtain information related to government activities”, especially in matters of defence, foreign policy or national security.
But the interest in this type of ‘silent’ attacks is not limited to espionage in these critical areas. “Almost any type of information can be exploited to gain an advantage in a geostrategic competition where we should not only think of cyber warfare but also of inter-business competition supported by states,” notes Joseba Enjuto, Head of Consulting at S21sec.
States also promote other types of ‘noisy’ attacks, which bring down services or affect the normal operation of organisations. “They seek to destabilise, cause unrest in the environment of the organisations and, in the case of strategic sectors, generate disturbances in the functioning of that sector, with the consequent damage to the affected citizens,” explains Enjuto.cyberwar Ukraine.
![]()
In addition, Manuel Pérez, director of Cyber Risks at Howden Iberia, points out that “in recent cases, states seek to finance themselves through theft and extortion of private companies”. For example, he points out that “the clearest scenario in this regard is the theft of cryptocurrencies”.
Thus, this state-sponsored cyberwarfare is no longer confined only to government institutions and agencies but extends to the whole of society. “The big problem posed by this scenario is that we all become potential targets, directly or indirectly, of this cyberwar,” says Emilio Jesús Sánchez Pintado, the lawyer in charge of IT at the law firm C&P Abogados. “Companies of all types and conditions, strategic infrastructures, public entities such as administrations or universities, and even individuals, have become potential direct targets of these actions promoted by states”, he adds.
But it is also true that state-backed cybercriminals prefer certain types of targets. “Most attacks are aimed at companies or sectors whose collapse could lead to social or political problems if successful,” says Hernández. He also points out that they are especially aimed at “strategic sectors whose availability has a great impact on the functioning of essential services for a country, such as health, the supply and distribution of raw materials, energy, food, security, etc.”. Exsel’s CEO adds that they tend to focus on “infrastructure, healthcare network, large data centres and government entities”.
Covered by cyber insurance?
With threats on the rise, more and more companies and institutions are looking to the insurance sector for solutions. According to a ‘Cybersecurity in Insurance’ report by GlobalData, the insurance industry will be earning $10.6 billion in premiums from cyber policies within three years, with a compound annual growth rate of 10% over the period 2020-2025.
However, it should be noted that insurance typically includes ‘acts of war’ or ‘terrorism’ among its exclusions. “Directly and/or indirectly state-sponsored attacks in war and non-war contexts constitute such massive loss scenarios as to make them uninsurable risks. Insurance companies have corresponding exclusions for this purpose,” the Hiscox expert points out.
In fact, Lloyd’s has recently announced that its cyber insurers will have to apply a clause excluding liability for losses arising from any state-backed cyber-attack, as reported by Füture.
Nieva believes that “insurers are limiting their potential damages under the assumption that protection against this type of cyber-attack is more difficult than against other traditional attacks and that they could potentially be massive and more extensive than other traditional cyber-attacks, which could compromise the insurer’s own livelihood if the attack spreads to different companies in a country”.
Faced with this situation, the president of Mapfre, Antonio Huertas, advocates the involvement of the states themselves in the protection against this type of attack. In this way, he calls for the creation of pools of insurance companies or other types of organisations “that assume the layers of coverage of greater risk” in the event of cyber-attacks backed by states, as reported by Estrategias de Inversión.
This solution would not be alien to us. In Spain, there is already an Environmental Risk pool and we have the Insurance Compensation Consortium (CCS), which provides cover for extraordinary risks, including claims arising from extreme weather events, which are becoming increasingly frequent.
Pérez also believes that such a solution should be sought. “The reinsurance market, in a large majority, refuses to cover terrorist acts, which leaves us in a scenario in which either the insurers themselves cover these risks with their own capacity or we must turn to the position of the CCS,” he points out. For example, he recalls that “this situation was already experienced in Spain with life insurance, which did not offer cover for terrorist attacks until, in 2006, the Ministry of Economy accepted that the responsibility for this cover lay with the CCS”.
The problem of attribution
The exclusion of state-sponsored attacks presents some complications. “The first is the particularity of cyber risk in that it is often impossible to trace, locate and identify the person or entity that carried out the attack. The second issue concerns the delimitation of the concept of ‘act of war’ or ‘terrorism’ in the policies. So, if an act of war or terrorism is defined by the type of actor who carries it out, how can we claim that a cyber-attack was an act of war if we are unable to identify the actor,” says Sánchez Pintado.
![]()
Likewise, the S21sec expert acknowledges that “the problem with this type of cyber-attack is attribution, which is often complex”. “Even if it is possible to obtain indications of authorship, being able to prove that these attacks have been promoted by a state is by no means simple. And if attribution cannot be made, exclusion would not be justified. Therefore, such exclusions are likely to give rise to much litigation between insurers and insureds because, in reality, the main difference between a ‘normal’ cyber-attack and one considered as an ‘act of war’ or ‘terrorism’ is the perpetrator, as all other aspects may be virtually identical.
This difficulty in determining authorship is at the very core of the conception of cyberwarfare. “To determine the origin of state-sponsored cyber-attacks we have to go back decades. The main reason for the birth of this new practice was the possibility of being able to attack another state and its infrastructure without the need for a formal declaration of war, with all that this entails in terms of sanctions, treaties and other reputational issues. For example, Russia’s first serious attack on Ukraine dates back to 2013, with the cyber-espionage operation ‘Armageddon’. The current paradigm shift is that these state-sponsored attacks are no longer solely targeted at other governments, but are spreading to private businesses and even individuals,” says Howden Iberia’s director of cyber risk.
Moreover, the line between an act of cyberwarfare and a ‘conventional’ attack is a fine one. “To take a recent example, the FBI, along with other US agencies, this year issued a Cyber Security Advisory (CSA) warning of the presence of a type of ransomware (Maui) targeting different organisations in the healthcare sector, which is being used by hackers hired by North Korea. Can an insurer prove that the Maui ransomware is a terrorist attack and therefore exclude it from coverage for its customers? The answer is unclear, as this same attack also has typical characteristics of a Ransomware-as-a-Service (RaaS), models that are usually sold in a pre-programmed form for subsequent execution by third-party hackers. So who executed it, is it an act of terrorism or not,” Perez asks.
Potential increase in litigation
As noted above, one possible consequence of the application of these exclusions could be an increase in the number of cases that will end up in court. “The amounts covered by cyber insurance policies are sufficiently high to justify such litigation,” says the head of S21sec.
And even more so if we take into account the complexity involved in certifying authorship. “There will be many occasions when it will not be possible to point the finger at a specific attacker, which can lead to ambiguous situations that can be interpreted in their favour by both the policyholder and the insurer,” says the Check Point manager.
Likewise, the Hiscox Spain cyber-risk underwriter admits that “there could be scenarios of uncertainty about the authorship of the facts, and this is where each insurer will act according to its values and interests”.
On the other hand, Howden Iberia’s Director of Cyber Risks warns that “as this is an insurance policy that is still unknown in detail by a large part of its contracting parties, policyholders may, in the event of an incident, not understand why they are not covered for this type of practice, increasing litigation”.
In any case, Satrústegui stresses that “the burden of proof is on the insurer”, who will have to demonstrate “reliably” that it is a state-backed attack for the exclusion to be valid.
Another possible consequence could be the withdrawal of the cyber insurance market. “If this pattern of attack continues to grow and becomes one of the main types of enforcement, policyholders may have the perception that their policy does not cover them properly and they will stop taking out their policy,” says Pérez.
![]()
Similarly, Nieva believes that “many institutions will think twice about taking out cyber insurance if they are excluded from compensation if the attack is carried out by a government and they have no way of proving it”. “Even if they are covered for attacks by private cybercriminals, if they are not covered for other types of attacks, and these are larger than the others, it won’t make sense to take it out,” she adds.
Official recognition, clear policies and transparency
One possible solution to resolve any disputes over authorship could be the creation of a body whose rulings would be respected by all parties. “Even if cyber security organisations are able to attribute authorship of a cyber attack, this attribution is still only the opinion of one company in the cyber security industry. As long as there is no recognised body capable of carrying out such attributions, legal uncertainty will remain. In the case of Spain, perhaps Incibe or the CCN-Cert could perform this function,” suggests Enjuto.
Perhaps the only way to mitigate this problem is to draft a clause that clears up all, or at least most, of the doubts. “It is important that the clauses stipulate very clearly the possible ‘grey areas’ that we can find in some situations or, otherwise, we will see cases in which the courts will be the ones to clarify the legality or otherwise of policies, compensation, etc.”, says Check Point’s technical director.
Losada agrees with him. “Insurance companies must be very clear and transparent when describing the scope of any coverage and exclusions. The language used in the terms and conditions must be very simple to avoid confusion, not only for this exclusion but for any other exclusion in any insurance product”.
Likewise, the specialist from C&P Abogados affirms that “the better the clauses of an insurance contract are designed, the clearer they are, the more appropriate terms are used to refer to the object of the insurance and the greater the precision in delimiting the situations that are covered, the less litigiousness there will be”. He also points out that “the more a cover is made objective, the less doubt there will be as to whether specific damages are covered or not, which ultimately also helps to reduce litigation”.
In this respect, he points out that some steps are already being taken in this direction. “The insurance industry has come up with numerous solutions, including the four new variants of the cyber warfare exclusion, published by Lloyd’s earlier this year.
“These exclusions contain terms that are more adaptable to the cyber environment and that leave out of the policy’s coverage those damages that “occur through or as a consequence of a cyber war or cyber operation”, for example. Likewise, an additional exercise of concreteness has been made in the delimitation of concepts such as ‘war’ and ‘governmental actions’, since they also play a fundamental role in the interpretation of these exclusion clauses,” he explains.
He also points out that “we find ‘model’ clauses that take as sufficient criteria to determine that we are dealing with an ‘act of war’ if, for example, “the government of a state, including its intelligence and security services” makes the attribution “to another state or those acting on its behalf”.
In any case, we must bear in mind that cyberwarfare is a new scenario, which is being shaped and redefined almost every day. For this reason, cyber insurance has to adapt. “It is clear that cyber risk insurance has not yet reached maturity due to the constant change in risk. This is partly due to the new players that are appearing and the constant improvement of attack patterns. We must give the insurance industry time to analyse and find the best form of coverage for each of the vectors that emerge each year. In the event that coverage appears without prior analysis time, we can have serious problems in the branch due to an uncontrolled claims rate”.
Moreover, insurance faces an additional problem: the lack of transparency of organisations that have suffered a cyber-attack. Many of them do not report them and are not clear enough about their extent.
Insurance actuaries adjust premiums based on risk, so they need reliable data to support their decisions. The lack of historical claims records greatly complicates their work and makes it difficult to set adequate and sufficient prices that allow insurers to meet their obligations without jeopardising their viability and to meet the solvency requirements set by the regulator.