Phishing Campaign Against Zimbra Users Discovered
ESET’s research team uncovers a massive phishing campaign aimed at stealing credentials from Zimbra users.
ESET experts have identified a wide-ranging phishing campaign that has been running since at least April 2023 and is still active. The main goal of this campaign is to fraudulently obtain the credentials of Zimbra account users. Zimbra Collaboration, an open source collaboration platform, is a popular choice for business communications in place of traditional email solutions.
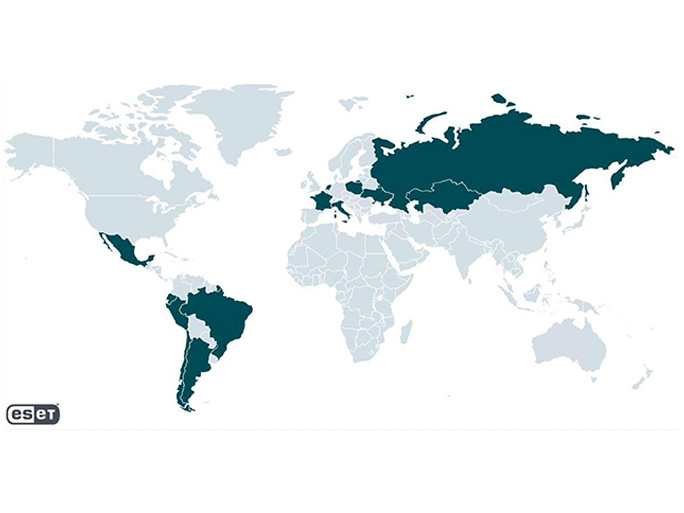
This massive campaign is focused on affecting small and medium-sized businesses, as well as government entities. Most of the targets are located in Poland, but organisations in other European countries, such as Ukraine, Italy, France and the Netherlands, have also been targeted. In addition, Latin American nations, in particular Ecuador, have also been targeted. Although this campaign is not particularly advanced from a technical point of view, it has managed to spread and successfully compromise organisations that rely on Zimbra Collaboration.
ESET experts’ thoughts
According to Viktor Šperka, the ESET researcher responsible for discovering the campaign, ESET believes that: “Criminals take advantage of the fact that the attached HTML files contain legitimate code, with the only telltale element being a link pointing to the malicious host. This makes it much easier to circumvent reputation-based anti-spam policies, especially compared to more widespread phishing techniques, where a malicious link is placed directly in the body of the email.”
“Target organisations vary; adversaries do not focus on any specific industry; the only thing that connects victims is that they use Zimbra. The popularity of Zimbra Collaboration among organisations that are expected to have lower IT budgets ensures that it remains an attractive target for cybercriminals,” added Šperka.
Attack pattern
The attack follows a pattern where the victim receives an email with an HTML attachment that leads to a phishing page. The deceptive message notifies the recipient about a supposed mail server update, account suspension, or other similar problem, and prompts the recipient to click on the attachment. Once the file is opened, the user is confronted with a fake Zimbra login page designed specifically for the targeted organisation. As the user fills in their credentials on the fake page, these are captured in the background and sent to a server controlled by the cybercriminals. This potentially allows them to access the compromised email account.
In addition, there is a possibility that the attackers have even accessed administrative accounts and created new mailboxes to send phishing emails to other targets. While the campaign identified by ESET relies heavily on social manipulation and interaction with users, there is a warning that this tactic could evolve in the future.