Report: How Security Ratings Can Help In The Supply Chain
Companies should know the security status of suppliers in the supply chain. But the assessment is complex. Security ratings as a service can provide support. An overview.
One’s own protection is not enough against supply chain attacks
More and more often, entire supply chains are affected by ransomware attacks, with consequences not only for the victims, but also for their customers or for other uninvolved third parties, according to the German Federal Office for Information Security (BSI).
Juhan Lepassaar, Executive Director of the EU’s cybersecurity agency ENISA, can only confirm this: “Due to the cascading effect of attacks on the supply chain, attackers can cause widespread damage, affecting companies and their customers all at once”.
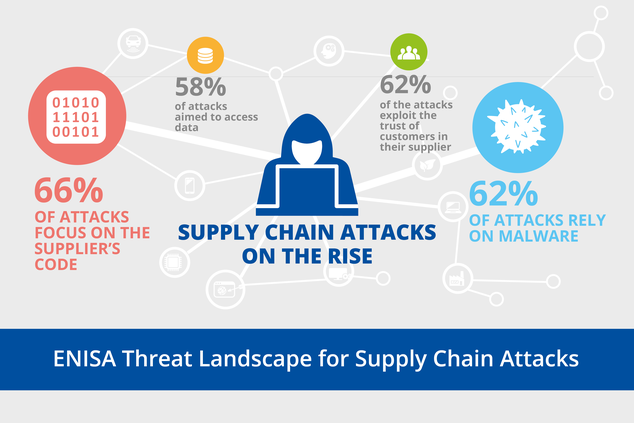
As the ENISA report “Threat Landscape for Supply Chain Attacks” makes clear, strong security protection is no longer sufficient for companies if the attackers have already focused their attention on the suppliers.
First, the cyber attacks exploit vulnerabilities in a supplier‘s security and then, in a second step, misuse the compromised supplier’s infected products, manipulated services or hijacked access authorisations to attack the customer company.
Security assessments for the entire supply chain must become mandatory
In order to counter the risks posed by supply chain attacks, security approaches such as Zero Trust are important. One must not simply trust a supplier despite a long-standing business relationship, which restricts the security controls over suppliers.
At the same time, the evaluation of a supplier’s security must become part of the procurement process and supplier management. At the latest, the rampant attacks on and via the supply chain make this more than clear.
However, how should a company be able to assess the security of a third party if its own security assessment can hardly be handled by the scarce security specialists?
As in other areas where resources are scarce, services can be of help here, too, so-called Security Ratings as a Service.
Security Ratings versus Security Certifications
A first approach to supplier security ratings is, of course, to ask for recognised security certificates for companies and products. This provides external confirmation that the supplier or the supplier’s products meet certain security criteria.
However, the underlying security audits of the certifier only take place once a year, for example. The cyber threat situation, the IT used and the vulnerabilities that become known change dynamically and very quickly. It is therefore certainly possible that even a certified company offers security vulnerabilities that attackers exploit for a supply chain attack.
The EU’s cyber security agency ENISA recommends “monitoring” supply chain risks. Ideally, information on a supplier’s security status should be available on a regular or even continuous basis.
This is where Security Ratings, which are also offered as a service, come into play.
What Security Ratings as a Service can offer
Market researchers at Gartner emphasise the importance of security ratings: “Cybersecurity ratings are becoming as important as credit ratings in assessing the risk of existing and new business relationships. These services will become a prerequisite for business relationships and a standard of care for service providers and procurers. In addition, the services will expand their scope to assess other areas, such as cyber insurance, due diligence for mergers and acquisitions, and even as a raw metric for internal security programmes.”
The market researchers’ recommendation is that “security and risk management executives should use security assessment services to provide real-time continuous assessment for internal assessments, procurement, partnerships and M&A activities”.
There are already many providers of security ratings services on the market. Examples are UpGuard, BitSight, SecurityScorecard, RiskXchange, RATINGCY, FortifyData and RiskRecon.
What Security Ratings do not do
A security ratings service can provide valuable information for assessing supplier security, although the data sources for and calculation of the security ratings differ from provider to provider.
However, it should also be clear that even a continuously calculated security rating will not guarantee that the supplier does not have a new vulnerability that is being exploited by an attacker.
A “good” score in a security rating does not mean that the organisation is secure, emphasised the security provider Palo Alto Networks (https://www.paloaltonetworks.com/blog/security-operations/security-ratings-vendors/). The US Chamber of Commerce, on the other hand, says: “As security ratings become more sophisticated, more organisations in the public and private sectors are using them to make business and risk decisions. As a key element of a robust security assessment programme, security ratings based on accurate and relevant information are useful tools for assessing cyber risk and facilitating collaborative, risk-based conversations between organisations.”
However, there are calls from the US Chamber of Commerce for more transparency and comparability in Security Ratings. To increase trust in Security Ratings, an industry-wide, common approach should be found. This should include the promotion of quality and accuracy in the production of Security Ratings, fairness in reporting, a coordinated process for assessing errors or inaccuracies in reported content, and guidelines for the appropriate use and disclosure of the ratings.
It seems that the Security Ratings themselves need a rating system so that they can be properly understood and better compared.